Topic Background

Lianyanshe
Crypto Newbie
03-17 01:18
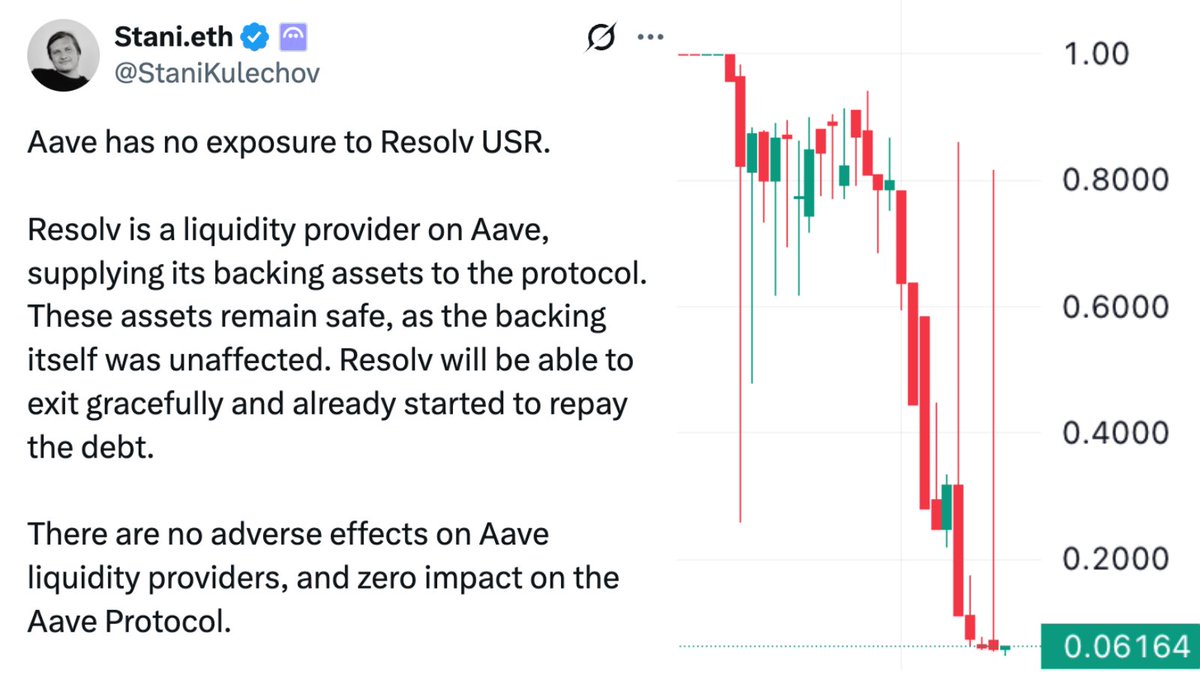
The recent $50 million AAVE transaction being squeezed led many to immediately suspect a hacker attack, lamenting how a single person's negligence could cause such a massive loss. However, this is an inevitable consequence of the old DeFi architecture. Your orders, transaction paths, and scale are virtually exposed on-chain; once visible, they are subject to bot pricing, targeting, and exploitation. The so-called free market often boils down to precise hunting on the public information flow.
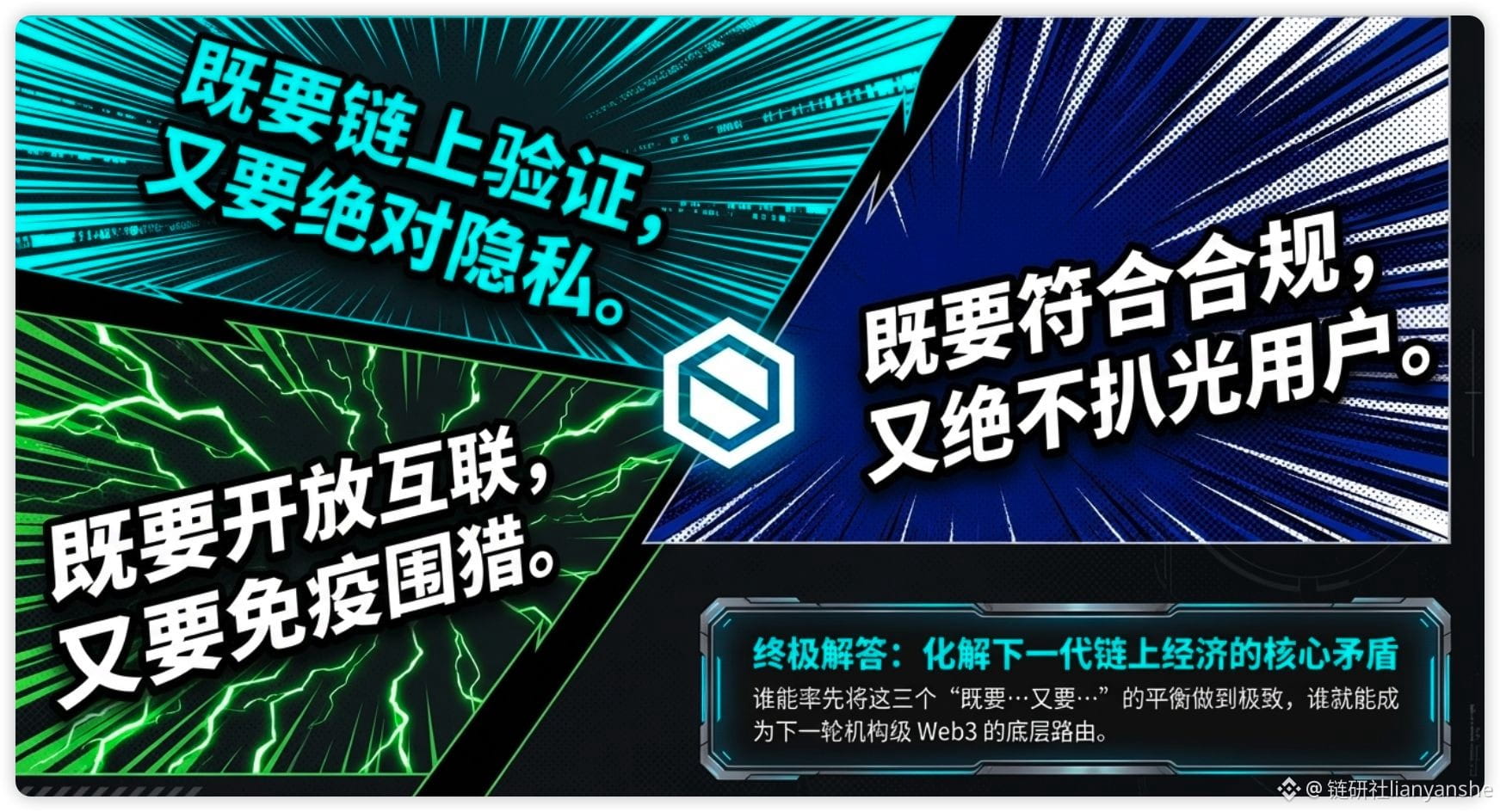
This is precisely where the true value of Midnight (@MidnightNetwork) lies. It doesn't sell anonymity, but rather rational privacy. Users can prove their compliance, asset authenticity, and transaction validity without revealing their identity, positions, or transaction details. It uses a two-state ledger and zero-knowledge proofs to achieve both verifiability and privacy simultaneously.
More importantly, Midnight isn't just a story. Its application scenarios include institutional DeFi, large-scale transactions, RWA, on-chain identity, medical data, and enterprise collaboration—any scenario requiring on-chain data but fearing information leakage is its primary battleground. The NIGHT + DUST design separates token value from usage costs, making privacy computing truly commercially viable.
The AAVE incident illustrates one point: the most expensive thing on-chain isn't gas, but the fact that your asset information is seen by everyone in advance. Midnight aims to solve what Web3 must do to move towards commercialization. It's not just another privacy chain; it's more like a future privacy operating system for Web3.
#night $NIGHT
BlockchainBaller
Crypto Newbie
03-16 21:19
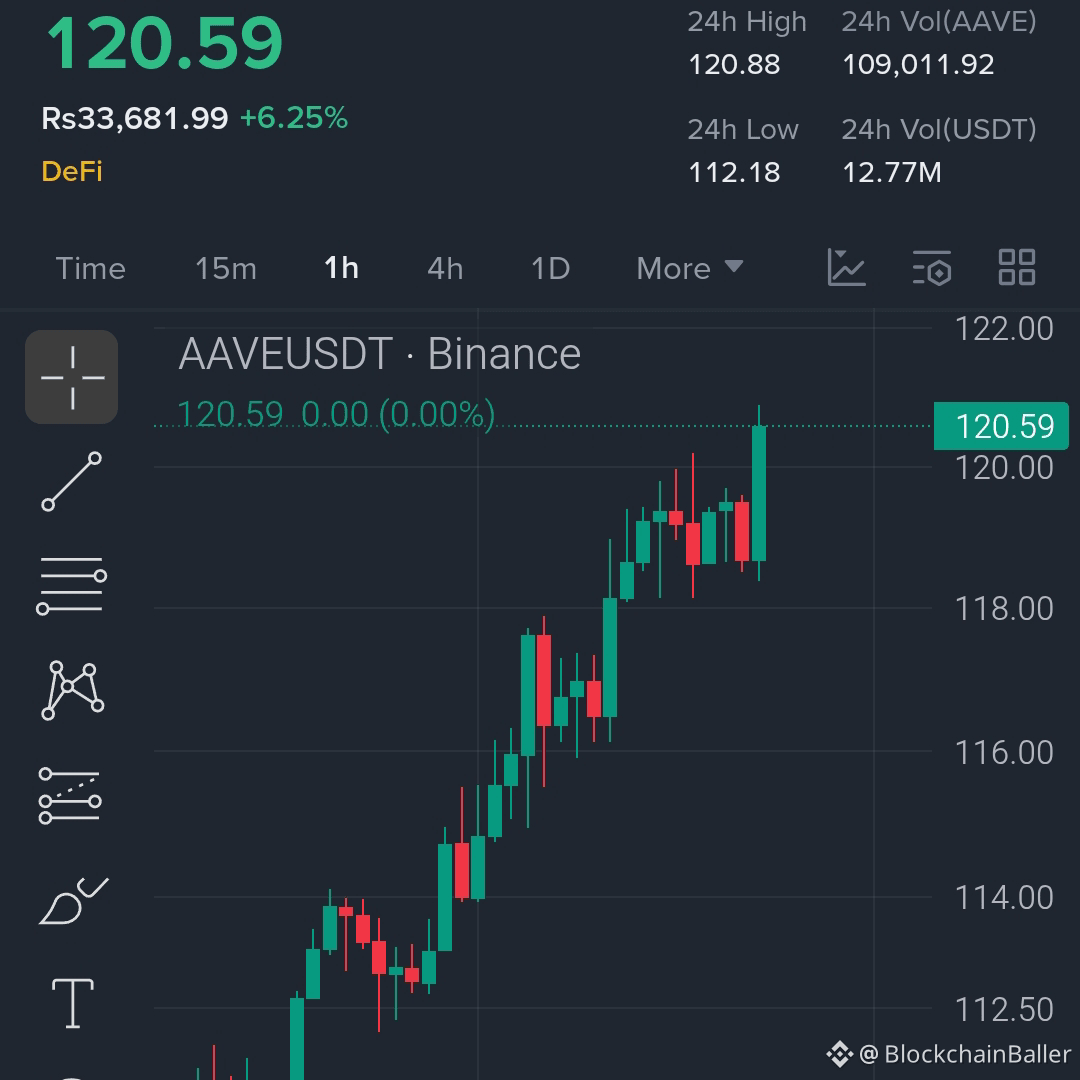
Congratulations to all those who trusted the $AAVE trading signals! 🚀
Hopefully you didn't miss my buy and long signals…
$AAVE is building resistance…the trend structure is clear, and buyers still dominate.
$AAVE — Long 📈
Entry Point: 118.5 – 120.8
Stop Loss: 112.9
Target Price 1: 124
Target Price 2: 128
Target Price 3: 134
Target Price 4: 142
Holding above 116, the bullish momentum remains strong.
If it successfully breaks through 122…the price expansion could accelerate rapidly.

Wu Blockchain
Binance
03-16 17:23
Venus Protocol has released a statement regarding the THE market attack. This incident affected the Venus Core market, while Venus Flux was unaffected. The team stated that this was not a flash loan attack; the attackers had been accumulating THE tokens over the past nine months and exploited a supply cap execution vulnerability in the protocol's legacy code to bypass the 14.5 million THE supply cap by directly transferring funds to the protocol contract. The attackers then manipulated the THE price using the low liquidity of the on-chain DEX, continuously amplifying the collateral value through a recursive loop (borrowing assets, exchanging them for THE to drive up the price, and then injecting them back into the market). Venus has currently suspended the THE market and set its collateralization factor (CF) to 0. As a precaution, it has also suspended collateralization functionality in the BCH, LTC, AAVE, POL, FIL, TWT, UNI, and LISUSD markets. Venus Labs is investigating with security partners and will release a full post-incident report.
BlockchainBaller
Crypto Newbie
03-16 15:15
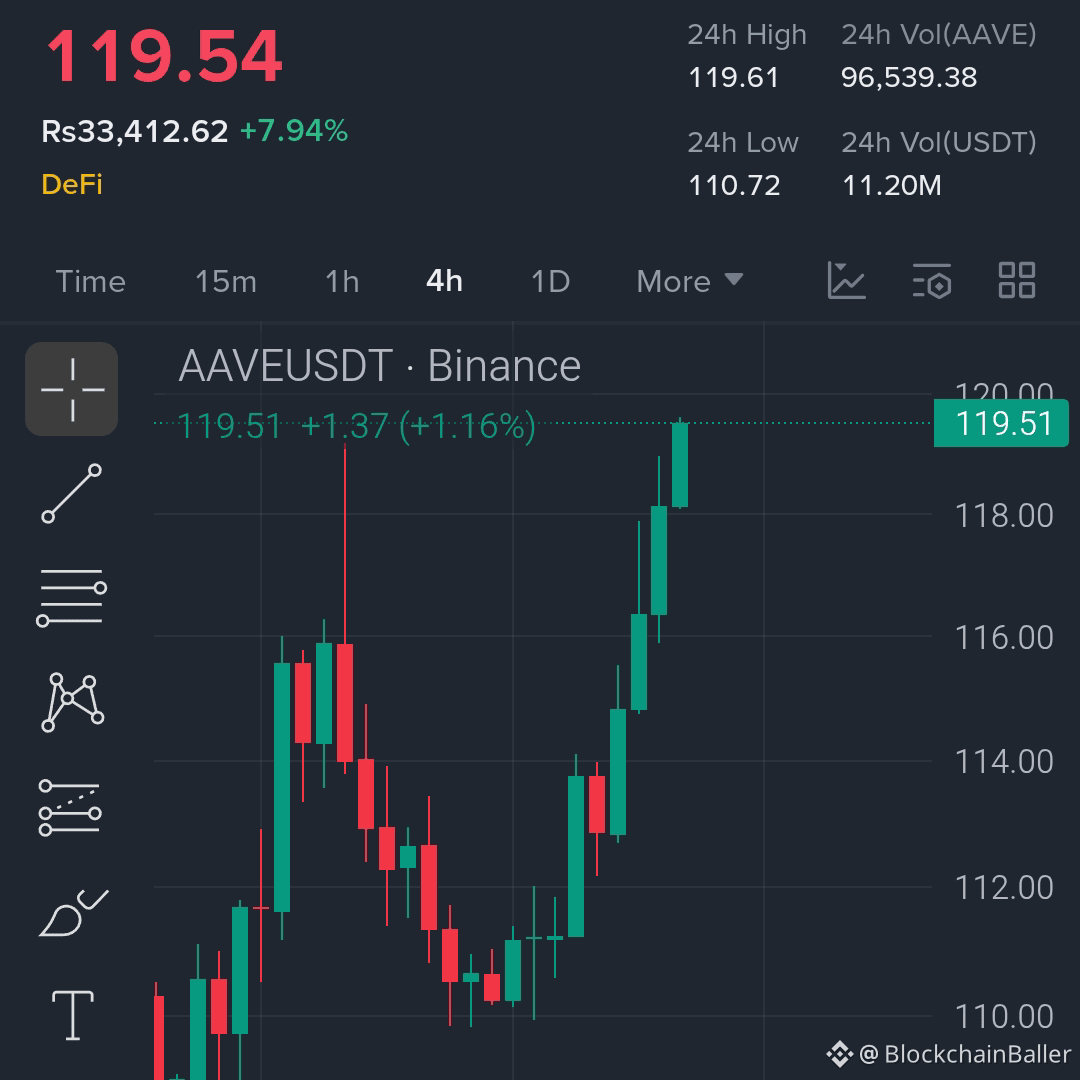
Stop scrolling down! Hurry and check back, don't miss this opportunity…
$AAVE continues to rise, while most are still waiting for a pullback…
$AAVE — Long 🔥
Entry Point: 117 – 120
Stop Loss: 111
Target Price 1: 124
Target Price 2: 129
Target Price 3: 135
Target Price 4: 142
Holding above 115, bullish pressure remains strong.
A break above 121 could quickly expand the upside potential.
Reversals reward those who act quickly… not those who wait.

Mars Finance
Crypto Newbie
03-16 09:34
🔔Venus Releases Preliminary Analysis of Hacking Attack Methods and Reduces Collateral Factor to 0 in 7 Markets
Mars Finance reports that on March 16th, Venus Protocol released an update on the abnormal activity in the THE liquidity pool. In addition to previously suspending THE lending and withdrawals, the collateral factor (CF) in seven markets has been reduced to 0. This preventative measure targets markets where a single user holds an excessively high proportion of collateral. The seven markets are BCH, LTC, UNI, AAVE, FIL, TWT, and LISUSD. All other markets remain unaffected and continue normal operations. The preliminary assessment of the attack method indicates that the attacker began slowly accumulating THE tokens through normal deposit processes starting in June 2025, eventually holding 84% of the maximum limit (approximately 12.2 million THE tokens). Yesterday, the hacker directly transferred THE tokens into the protocol contract, instantly boosting the supply and creating a massive amount of collateral. The hackers then engaged in recursive price manipulation, exploiting the extremely low liquidity of THE on-chain coupled with TWAP oracle delays. The cycle involved depositing THE, lending out other assets, using the lent assets to buy more THE on-chain, and waiting for the TWAP oracle to update and drive up the price. Venus stated that it remains committed to transparency and will release a full report after the investigation concludes.

BlockchainBaller
Crypto Newbie
03-16 04:57
$AAVE has quietly regrouped after its sharp drop…
Forming higher lows…buyers are returning to the market.
If the resistance level is broken, momentum will quickly expand.
$AAVE — Long 🔥
Entry Point: 113 – 116
Stop Loss: 108
Target Price 1: 119
Target Price 2: 123
Target Price 3: 128
Target Price 4: 136
Holding above 112 indicates strong upward momentum.
Early entry always feels uncomfortable…but the real moves often start here.


Wu Blockchain
Binance
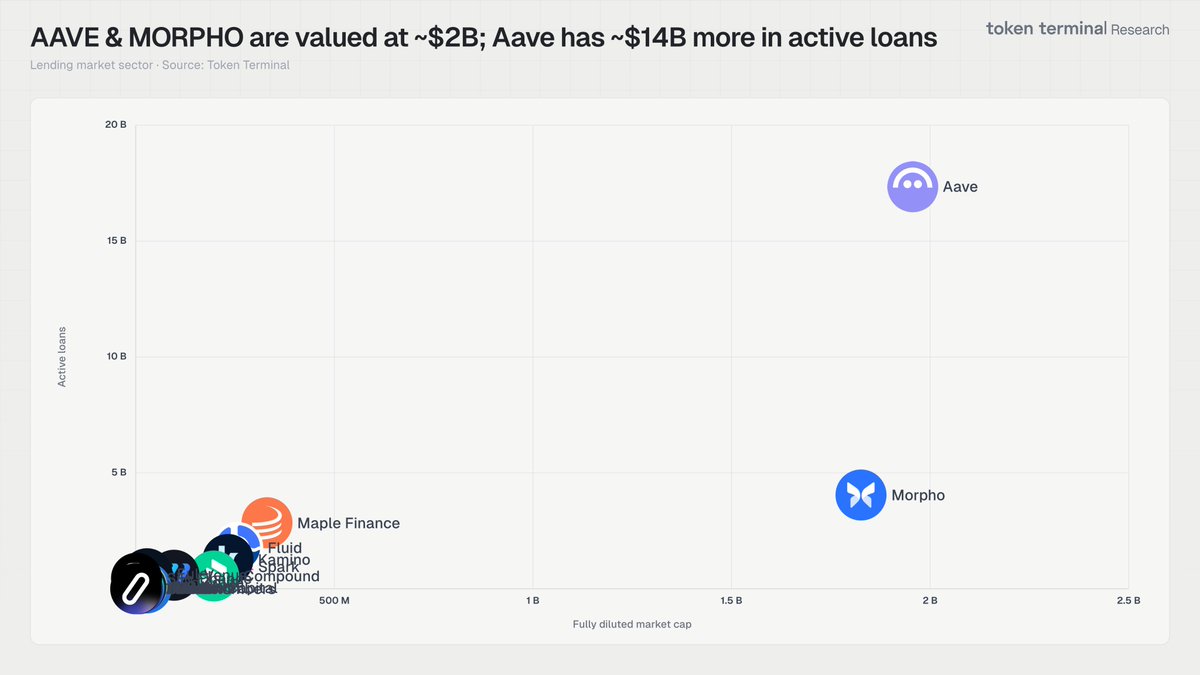
03-15 10:13
According to Wu, a Snapshot page shows that the Aave community is voting on an ARFC proposal to reduce the annual AAVE buyback budget from approximately $50 million to approximately $30 million, with a current support rate of 99.37%. The proposal states that Aave DAO lending fee revenue has declined by approximately 25% from its peak, with January 2026 revenue at $7.95 million, lower than the $13.5 million in January 2025; meanwhile, the 2026 operating budget is projected to be approximately $190 million, higher than the approximately $142 million in annual revenue in 2025, indicating a structural deficit. If the ARFC passes, the proposal will proceed to the formal governance voting stage of the AIP.